- Every dad should build their toolkit with theses 10 DIY gadgets
- Broadcom grows revenues by 20% following VMware purchase, as customers fume about subscription costs
- How global threat actors are weaponizing AI now, according to OpenAI
- The viral Air Purifier Table is my smart home's MVP (and it's on sale for $179)
- Grab the Galaxy S25 Edge for $170 off and get a free Amazon gift card - but act fast
Navigating DORA (Digital Operational Resilience Act) with Secure Workload

Over the past decade, the cyber threat landscape has undergone a significant transformation, escalating from isolated attacks by lone wolves to sophisticated, coordinated breaches by state-sponsored entities and organized crime groups. During this period of change, cybersecurity has often been a secondary thought for enterprises, frequently addressed through reactive measures insufficient to counteract such advanced threats. However, we’re witnessing a pivotal shift, predominantly driven by regulatory bodies, toward establishing harmonized guidelines that can keep pace with the dynamic nature of cyber threats.
The Digital Operational Resilience Act (DORA) represents one such proactive stride in this direction. Targeted at the European Union (EU) financial sector and built around five core pillars, DORA advocates for a risk-based framework that enhances the sector’s capabilities to prevent, respond to, and recover from cyber incidents.
How can you leverage Secure Workload to prepare for DORA?
While DORA does not dictate precise technical requirements, it provides the groundwork for a risk-based shift in cybersecurity. Secure Workload serves as a pivotal tool in this transition, enabling organizations to understand risk, prevent and mitigate risk, and report risks associated with their application workloads.
1. Understanding Risk
To understand risk, you must have visibility to know what is happening in your environment. Secure Workload delivers in-depth insights into how your workloads communicate and behave, including identifying any vulnerable packages installed. You can quickly answer questions such as:
- “Are my workloads utilizing approved enterprise services for common services such as DNS or NTP?”
- “Am I vulnerable to a specific vulnerability?
- “What is the risk of that vulnerability” Is it easily exploitable?
- “Are my workloads using insecure or obsolete transport session protocols and ciphers?”
- “Are my financial application workloads communicating to non-production environments?
- “How is my financial application communicating to external dependencies?”
- “Is it communicating to malicious networks?”


2. Preventing and Mitigating Risk
Once the risk is understood, it is time to act. This action can take the form of proactive controls and compensating controls.
- Proactive Controls: Secure Workload microsegmentation policies allow you to create fine-grained allow-list policies for applications by discovering their dependencies. Additionally, guardrail policies can be established to restrict communications from risk-prone environments to your production workloads, such as non-production cannot talk to production workloads, or the PCI Cardholder Environment cannot talk to PCI Out-of-Scope or perhaps OT network cannot communicate with the data center, allowing to contain lateral movement and reduce the blast radius.

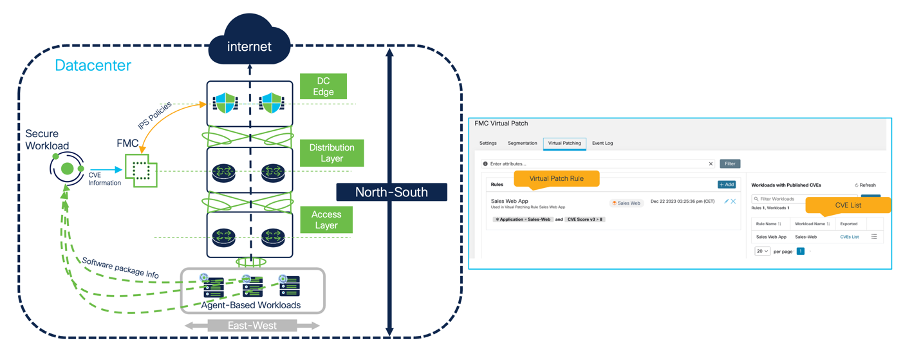
- Compensating Controls: Even in the worst-case scenario, where a new zero-day vulnerability is disclosed or ransomware hits the organization, Secure Workload can rapidly act on this and restrict For example, you can quarantine a workload communication based on multiple attributes, such as CVE information, CVE Score, or even the access vectors access vectotr assestment.You can also choose to leverage Virtual Patch through the Secure Firewall integration to protect your workloads against exploits while the patch is applied. Even in the scenario that a workload changes its behavior (e.g., from trusted to untrusted due to an intrusion event or malware event) you can leverage Secure Firewall intelligence through FMC (Firewall Management Center) to quarantine workloads.

3. Reporting Risk
DORA mandates to report major ICT-related incidents to relevant competent authorities. Because of this, reporting becomes a paramount process within the organization. Secure Workload offers multiple options for reporting, ranging from near real-time visualization dashboard and reports to detailed point-in-time retrospectives of incidents.
- Security Dashboard: Provides a high-level overview of the security posture and hygiene of the environment.
- Vulnerability Dashboard: Displays current CVEs within the environment along with a detailed assessment of their potential impact on confidentiality, integrity, and availability. Additional metrics such as risk score, exploitability, and complexity are also included.
- Reporting Dashboard: Presents a detailed view tailored to specific roles like SecOps and NetOps. An important capability to mention here is how the security summary maps to a modern risk-based approach to detect adversaries MITRE ATT&CK framework. Secure Workload has multiple forensic rules mapped to the MITRE ATT&CK TTPs (Technique, Tactics, and Procedures) allowing one to identify an adversary and follow every single step taken to compromise, exploit, and exfiltrate data.


Key Takeaways
While navigating the requirements of DORA may seem daunting, the right tools can revolutionize your organization’s approach to Cyber Resilience with a risk-centric focus. Secure Workload can be instrumental in facilitating this transformation, enabling your organization to achieve:
- Strategic Cyber Resilience: Secure Workload can be a strategic enabler for aligning with DORA’s vision. Transitioning from a reactive cybersecurity stance to a proactive, risk-based approach, prepares your organization to anticipate and counteract the evolving cyber threat landscape
- Comprehensive Risk Insights: With granular visibility into application workload communications, dependencies, and vulnerabilities, coupled with the implementation of robust microsegmentation and compensating controls, Secure Workload equips you with the capabilities to not only understand but also to effectively mitigate risks before they materialize into breaches.
Want to learn more? Find out more at https://www.cisco.com/site/us/en/products/security/secure-workload/index.html
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Security on social!
Cisco Security Social Channels
Instagram
Facebook
Twitter
LinkedIn
Share:

